Misinformation - Can ‘Multi-Entrance’ Deployment Replace ‘Multi-Layer’ Deployment?
Misinformation, once integrated into our long-term memory, becomes very difficult to correct, particularly when it was spread by big names. Informed consent must be respected. Misinformed consent must be corrected and disinformed consent indicted however embarrassing it may be.
There is a voice claiming that deploying biometrics with a fallback password on a mobile device makes a 3-factor authentication (‘what your body features are’, ‘what you know’ and ‘what you have’). Even when the user gets falsely rejected by biometrics and required to use a password as the fallback means, the user is still protected by the 2 factors of ‘password’ and ‘device’, so the failure of biometrics does not mean the decrease of security. This is their voice.
However, a straightforward 2-factor authentication made of ‘device’ and ‘password’ would have been more inexpensive, easier to implement/manage and more secure. Multi-Entrance solutions cannot displace Multi-Layer solutions..
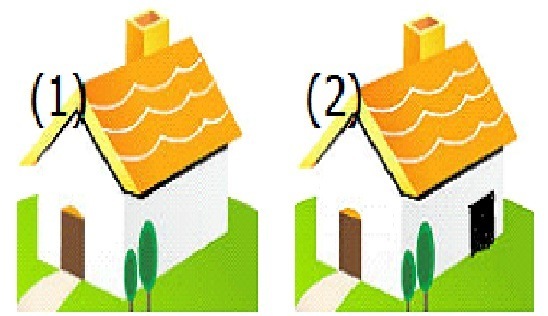
The distinction between 'multi-layer' and 'multi-entrance' deployments (in-series/AND/conjunction versus in-parallel/OR/disjunction) of two/multi factors is plainly demonstrated below.
Incidentally, tech media seem busy arguing on which biometrics offers better protection than the others. But it is all nonsense from security’s point of view. All of them provide the level of security lower than that of a password-alone authentication in cyberspace. Tech media should instead ask why security-lowering measures have been touted as security-enhancing solutions.
Biometrics in two/multi-factor authentication: Biometrics could be recommended for better convenience, but must not be recommended where security matters.
Hitoshi Kokumai の記事
ブログを見る
I would like to take up this somewhat puzzling report - “Google advises passwords are good, spear ph ...

Some friends directed my attention to this news report - · “Biometric auth bypassed using fingerpri ...

Today's topic is BBC's “Facebook to end use of facial recognition software” · https://www.bbc.com/n ...


コメント