Cryptography and Expanded Password System
![HTEDI4Z JUTE 4 GIOZIUSPRR SJL E320 T9 14 G0 AKT |NGERS THOU JEI0E1 P93 IIQN SOLMPUICL Wh SVERL T 1G SKY YR YR)
£1 mn BINT $C HL AKRETES WIC 1 IAT 2 BAITEBOVY YP 2302 POTOLOIORTL AUP OPVRNTI LIMOS LK 84 Tn
CH03 1) )F ANPRCYGADL 1 LMELORD JT IORI PNSIRIQ] 7 VDE TOTAIGRL 1 GRINCAL TUARNP RANE 790 7CA TN | AC RCH
FLTOQANPY | WAS 189) J ERCATNDN 1 LUT | TMNT J41YEORBNG 7 IVEK TRACGLDS 11 112031 78 HT ALD 170TH)
Sn HTS 161891 KI ROCL TRRICATONE J T08 1 64XT Lie? 7X §L MEVRRBMCA Xm 84) 70.11
C430579100TVFVA 1452071 VOLT 1GL PV vi88.4 0377 AMV 1 Y3CY S99 LAL KOOL P83 JAR IPF [C91
SCA CA) EDT RPBE 76 1 GK BOA KT 1D 14 TYRANT TL TR BOL SN TN 994411 ©
TI QF KPAVRONT TEA DUK 06 SN VAC TROY ZOU ON LG IGINOT 2X8 TENE dr
WY) 7439 36R1OHMGVI LR) Tf KC LAB KARBOCCY PION] 26 TV AVES Sut w 2 4
4 LL MH ZW YET TKETHIL 2650 QE VS TW TUG NRY BT ION 1040 NT HAL LIAT BNL 1 HE
PCB LGTY ISH BROT RAL R102 IL NAL: JOU STVYRR] 164 GKS INCOGRDT: EOY Rar RNC 9
TL OP OM IOTK LL BCORIKI NIOBATE CHR PANG 05 DANO LV? 2 ANI) PVE TRD TH LINC PAT
#2 LATS VRID XE BL TTROD LLGK JON: XYANQAL TLE 20TBS 190% TRQUAIDOR JTL 1< bn x
9 9900 T99 £ XMGLACU PDQ) S YING) [HLA ICG TON 7onPO7 TH CONRANS TGEKS JARS IC B
TART GOB VABATIAAT SGI TIS F 1124.26 6.JAGY1 IREALOT OR BIW TF L008 Jot
x RRARSD VL THQI HAE 1¥ 119 KXVVA) DRT SLMEMN SX) 1 79Y ORF | SBT 1.19 QA THOR AL HA%4N 11 11
A BABA] SOA IF CV IGIANP SOG JL RTABRGH )1 SVR) TSPP4) XGVY IOP LKRY I IAPTRIG TIT 10
ML OTHIKT7O7ENIR JF ISAO LICOP® TORCTEXBIOTHN JT 1QV SBT INYSXINGHTHNT IL FAITCHRSIT11X0C 100
7 TOIG 1108 IV] ICAP BMY VAM £336 HT TOK SEC 18207480 1130 TMI 1BDPOL 714TH} 1430 CG00 77111 vn
LHL CRD D828 INGE O61 F 38 TWIG1 TI 78 GANIKE | ZRRAGPTUTERE® 105 P 10E LE 37 TEI ROAY BGMIOR 1 INOTOLIXVES 1EVES ENE
CG TG) TREE SAGER SVU ADAGE TABTXBYG TL GRICE 75PL1 SHAGOCHIVG WS UTTRAM AVS TRY) 7011 4300 VBN1 34 1 VTP
13 GumAB ear 90
SFSATLEY 14541 MEA OP AGE T | SRARBASGAKAME 3.20% IAT TAN] EUG 4659 JORDERAT SCO TCARBKLOT BTV 3 THC YF LIMGIXOP 1C 3 1F 865m | ACA x3
YCHT IVE ZAKS 7 1PTGAOTY AT DZUUNS JXIQIDICE SORT 7 1598 TVA7 I TVPORVING HER) IVF JA OT 1 1GKTQROIMIPTSHmIONN 14 34K] LENOIGEE G44
AREAL JL A TREATS 7611 V07 TLIOABOT S707 19 14TVEO0Y 14143 WMHOOMR/LINTQINADE 7 7C T11 | SLARSVE 0 14 GOAL LMEOX | Wb: 76407C RIAD) C
COS 13 TORORAT G6 INTRO LP T0100GA SGT TCR IAS E 19PMAKIN LACH ms 62 97S Sem2 IGOR] $71 $55.1 HALL INDY SSBEY 874 163CHL 64 1450S 117 V-
CULO) TBCAT IAT THON 25.201 CHCONTYIV IO INT 6 JG YYINY ICRGHTORT S3CIRAT TY IAD JK. IMAL ITZ) JKQm RF GIPRAY JAF TAT TKD SIVENTF £43 1CAX , 1079T)
71 700K MWR VOROQAKLUR KT3 1.530 1A7LNB1G17 10ARY) | FEANTLI IMOTY 2 LORAIN W0 4175 VRAL LA TX LMI SABR 11X01 OV2RSGH XJ OWR, 431670 711M
BH 27S NT 21 M1 F GUIS 04 I0U INL O IVAT O76 SETUP JPO4S XATZRMEDS TQUCOUKLEL INE EKD7VIXE AMS LOUT#NESC 11 796 V IW I0S SC HC RAAR PSV 3 54000
EE a a a ane Ee](https://contents.bebee.com/users/id/13855668/article/cryptography-and-expanded-password-system/4dfeb8a8.jpg)
Prof. Hideki Imai, who pushed my back to move ahead confidently in 2001 when he was the chair of Japan’s CRYPTREC, used to emphasize repeatedly how critical it is to get the credential data hashed whether online or offline. It is from him that I learnt about Deffie-Hellman Key Exchange, Elliptic Curve Cryptography, etc.
We jointly tried the methodology of using the high-entropy credential data generated by
Expanded Password System (EPS) as the seed of RSA key pair; the user's private key does not physically exist anywhere in the universe, but it can be re-generated in-the-fly out of the images that the user picks up for authentication for each login. It proved to work on the internet.
Thereafter, we took up the experiment of incorporating EPS into PAKE. We were able to demonstrate that it worked with no friction in the lab environment.
These projects, sponsored by government agencies, were completed in 2003 – 2004. In retrospect, we seem to have started these forward-looking projects a bit too early.
Cryptography helps EPS, and EPS helps Cryptography.
![“Expanded Password System
Bans & Only I can select all of
BL] them correctly
Broader choices with both images and characters accepted
i
Easy 10 manage reletons between accounts and corresponding passwords.
&
Torturous login is hstory. Login is now comfortable, relaxing and heaing
SRO
250
8](https://contents.bebee.com/users/id/13855668/article/cryptography-and-expanded-password-system/d0bb9fbb.jpg)
Seemingly Fatal Drawbacks of Pictorial Password – Shoulder Surfing & Low Entropy
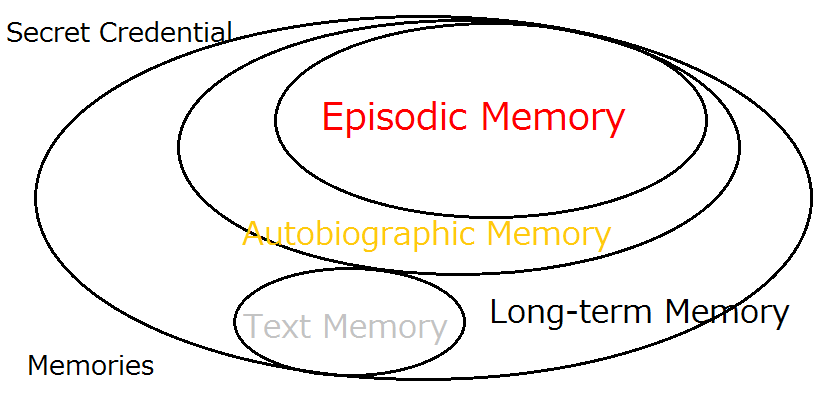
We have been advocating Expanded Password System that accepts images as well as texts from 2001. We have since kept hearing our proposition blamed for two major ‘drawbacks’ of using images – Shoulder Surfing and Low Entropy. So many people are still misguided to take it for granted as if it were the case.
The fact is that threats of shoulder surfing can be mitigated with ease by some simple techniques - images to get shrunk prior to tapping, texts allocated to images for quiet typing and so on at the end of developers, with the simplest solution being just looking around you before tapping the images at the end of users. How can it be a fatal drawback?
Another seemingly serious problem of low entropy can be eliminated at the end of developers without giving any extra burden on users.
With Expanded Password System, each image or character is presented by the image identifier data which can be of any length. Assume that your password is “CBA123” and that the image ‘C’ is identified as X4s& eI0w, and so on.
When you input CBA123, the authentication data that the server receives is not the easy-to-break“CBA123”, but something like “X4s&eI0wdoex7RVb%9Ub3mJvk…………..” which could be automatically altered periodically or at each access where desired, all without involving users.
Passwords of sufficient entropy, if properly hashed, can stand fierce brute force attacks. How can it be a fatal drawback?
Hitoshi Kokumai の記事
ブログを見る
Today's topic is “Microsoft Exchange Autodiscover protocol found leaking hundreds of thousands of cr ...

The quantum computer held in a bad guy’s hand is indeed a big threat. So is the artificial intellige ...
There is actually a valid methodology that enable us to maximize the entropy of the secret credentia ...


コメント
Hitoshi Kokumai
5年前#3
Hitoshi Kokumai
5年前#2
Thanks Zacharias. I am sorry to be very late in coming back to you. I had missed your comment. I would like to believe that cybersecurity people will come to comprehend the meaning of our proposition when they have come out of the pitfall of wrongly perceived security effects of password-less authentication and password-killer biometrics. As for the subject of cryptographic keys, you might be interested in my recent article "Account Recovery by Expanded Password System".https://www.bebee.com/producer/@hitoshi-kokumai/account-recovery-with-expanded-password-system
Zacharias 🐝 Voulgaris
5年前#1