Big Myths in Digital Identity
(A) What can we make of ‘Password-Dependent Password-Killer’?
(B) What happens where a factor to be enhanced gets removed?
(C) What does ‘PIN-dependent Password-less Authentication’ mean?
- --------------> ’Illusion of Safety’ and 'Cognitive Dissonance'
(A) Security professionals would be advised to refrain from referring to the biometrics as if it were a valid security factor equal to the passwords/PIN and the certified token.
The token and the password/PIN can be deployed on its own and also with other valid authenticators in the security-enhancing ‘multi-layer’ methods, whereas the biometrics generally cannot be deployed on its own. It can be deployed only in the security-lowering ‘multi-entrance’ methods along with a fallback measure.
When referring to the use of biometrics, security professionals should stipulate appropriate caveats to consumers; “Biometrics used with a fallback measure (Password/PIN in most cases) provide the security lower than that of the fallback measure” as outlined in this video.
So much money invested and so many products sold, it may be hard to admit ‘It brought down security’. But, it’s never too late to return.
(B) Security professionals would be advised to refrain from implying that better security can be achieved by removing the password. What can be achieved by removing the password is increased convenience, not security!
While detrimental features should be removed, insufficient ones can be supplemented and enhanced. Mixing up the former and the latter, we would witness a very bizarre situation. What is to be enhanced gets removed, with the 'blind eye' toward a specific frailty that afflicts.
More significantly, the password-less (will/volition-less authentication) is not consistent with the value of democracy. It would be a 1984-like Dystopia if our identity is authenticated without our knowledge or against our will,.
Those who have supported the concept of ‘better security achieved by removing the password’ may find it very hard to withdraw their remarks. But, it’s never too late to return.
By the way, this is a simple thought experiment.
Where the password was kicked out, security providers would be given only the token and the biometrics as security factors. Biometrics requires a fallback measure against false rejection. With the password removed, nothing but the token could be the fallback measure. Then system designer could have only the two choices as follows.
(1) authentication by the token alone, with an option of adding another token. Its security effect is highlighted in this cartoon published14 years ago,
(2) authentication by the biometrics deployed in ‘multi-entrance’ method with the token as a fallback measure, security of which is lower than (1) irrespective of however called it may be, with an option of adding another token.
A barren desert!
(C) As discussed earlier, removal of the password from the digital identity, makes it just infeasible for anyone to come up with a reliable identity authentication system
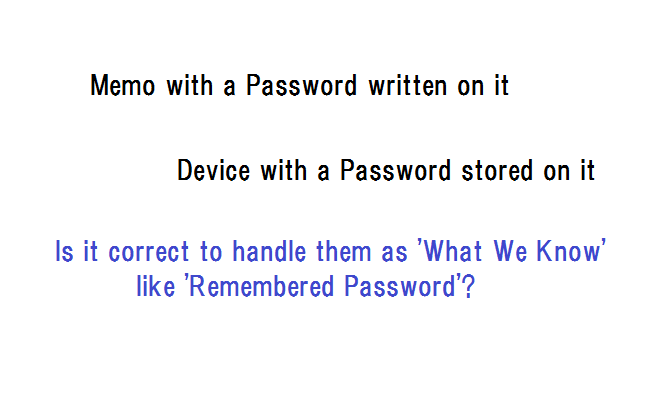
It appears that some people thought that this predicament could go away if they declared that the PIN was not the password. Say, the password should be removed but the PIN could stay for use on its own or as a fallback measure for biometrics.
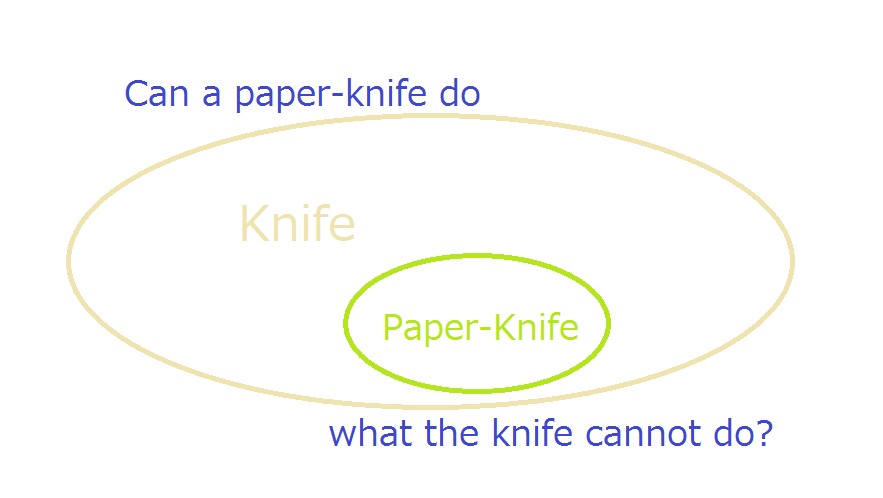
In this world where we live, the PIN is no more than a weak form of numbers-only password. Therefore, when the password (superordinate/generic concept) is removed, the PIN (subordinate/specific concept) is also removed. To the contrary, in a parallel world where those people live, the PIN (subordinate concept) can do what the password (superordinate concept) cannot do, as a paper-knife should be able to do what the knife cannot do.
Security professionals would be expected to firmly reject such an unearthly conception as a ‘PIN-dependent Password-less Authentication’.
Then, we will be free from ‘Illusion of Safety’ and ‘Cognitive Dissonance’
< Related Articles, Video and Cartoon >
- Digital Identity and Democracy
https://www.bebee.com/producer/@hitoshi-kokumai/digital-identity-and-democracy
- Quantitative Examination of Multiple Authenticator Deployment
Distracters in Digital Identity
https://www.bebee.com/producer/@hitoshi-kokumai/distracters-in-digital-identity
- Intriguing Evolution from One to Two and Back to One
https://www.bebee.com/producer/@hitoshi-kokumai/intriguing-evolution-from-one-to-two-and-back-to-one
- Biometrics in Cyber Space - "below-one" factor authentication
- Entangled thinking makes everything more entangled
"Hitoshi Kokumaiの記事
ブログを見る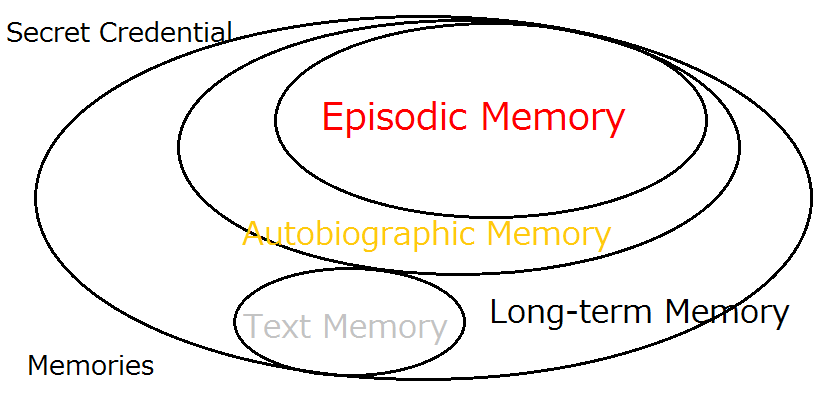
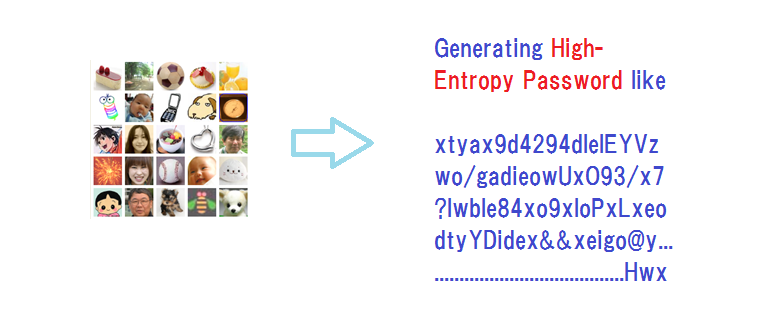
There is actually a valid methodology that enable us to maximize the entropy of the secret credentia ...
I got interested in this article -on the password problem · “Tech Q&A” · https://www.unionleader.c ...
We’ve come up with a slide presentation for “Bring a healthy second life to your legacy password sys ...
この職種に興味がある方はこちら
-

部品の組立/検査
次の場所にあります: Whatjobs JP C2 - 5日前
株式会社日本技術センタ一 Osaka, 日本**採用詳細**: · **部品の組立/検査**: · \3月スタート/高時給1320円☆日勤のみのお仕事部品の組立/検査をお任せ♪日払い・週払い対応◎車・バイク・自転車通勤OK☆ · **募集項目**: · **勤務先**: · 株式会社日本技術センター · **職種**: · 部品の組立/検査 · **雇用形態**: · 派遣社員 · **仕事内容**: · 大量募集中の今が大チャンス · クリーンルーム内での作業をお任せ♪ · コツコツした作業が得意な方必見です · 【具体的なお仕事内容】 · 1組立 · 製品のサイズは手のひら大(高さ10cmの筒 ...
-
事務・ピッキング作業員
次の場所にあります: Talent JP C2 - 1日前
福山フレッシュコンベア株式会社 Okayama, 日本仕事情報 · ● 仕事内容 ・事務所PCへの商品欠品登録作業などの事務作業・チルド商品の入出庫・ピッキング軽作業 ●仕事の流れ 事務所PCでの商品の欠品登録など簡単な事務作業。電話受付、対応。冷蔵倉庫内での、チルド商品の仕分け作業応援。最新鋭のデジタルアソートシステムを導入。初めての方でも迷わず、楽々簡単に出来る軽作業です。 ●主婦・フリーター歓迎 あなたのライフスタイルに合わせて働くことが出来きます。9時からの勤務で短時間(4時間以上)可能。 ●福山フレッシュコンベア 2020年4月より、東証1部上場企業の福山通運グループの一員として新規参入地域に根 ...
-

スシロー 姫路飾磨店
次の場所にあります: Talent JP C2 - 7分前
AKINDO SUSHIRO Himeji, 日本仕事情報 · ● 仕事内容 開店前のフロア清掃は、お客様をお迎えするにあたりとても大切 · なお仕事です。開店後は、お客様のご案内・お会計・お持ち帰り · 商品の受付と受け渡し等のお仕事があります。基本的に注文は · レーンから流すので、お寿司を運んだりすることはほとんどあり · ません閉店したら、片付けやレジ締めをしてもらいます。 ●主婦(夫)の方、活躍中 勤務は週2日から。シフト制なので、時間の融通が利きます。 · 家事の合間や保育園のお迎えまでなど、都合のいい時間を有 · 効に使ってお仕事してください。主婦(夫)の方は、 · 扶養内での勤務や、夏 ...

コメント