What Biometrics Vendors Tell Us versus What NIST Tells Us
![Same-Visit 0.34% 0.68%
Transactional | FNMR @ 0.10% FMR] FNMR @ 0.01% a
Cross-Visit 1.94% 2.77%](https://contents.bebee.com/users/id/13855668/article/what-biometrics-vendors-tell-us-versus-what-nist-tells-us/4d457d49.jpg)
I recently posted “Comfortable Biometrics Ecosystem” In its aftermath, I learnt from one of my LinkedIn contacts that NIST had publicised test results of some biometrics products.
Above is a screenshot of the test result of a biometric product, of which the accuracy is boasted by the manufacturer as ‘FNM (false non-match = false negative/false rejection) rate being 1 out of 100,000 at FM (false match = false positive/false acceptance) rate being 1 out of 10 million”.
The huge difference between what the manufacturer tells us and what NIST tells us is mind-boggling. I cannot help but to be very curious about which set of figures have been presented to their clients.
The NIST paper is available at https://www.nist.gov/system/files/documents/2016/11/30/thieme_michael_performance_testing_of_emerging_biometric_technologies.pdf
We looked for newer results for the same products but were not able to find any.
False sense of security has only been benefiting criminals, hasn’t it?
Biometrics has continuously contributed to providing a favorable environment to criminals, not to citizens, for nearly two decades and the public has been misled to believe that biometrics has provided better security for citizens. This false sense of security might well keep causing huge damages on our societal life for many more years unless somebody speaks out articulately.
Over several years we have repeatedly made clear that biometrics brings down security to the level lower than a password-only authentication where it is used together with a password in a ‘multi-entrance’ deployment, as against a “multi-layer” deployment.
We have received not a single logical or evidence-based refutation, which led us to suspect that the biometrics guys love a one-way propaganda but hate the exchange of opinions.
They might be prepared to allow people to debate on ‘spoofing’ and ‘data leak’, because they could counter these debates by talking about the eternal endeavor of improving technologies. But it looks like they are aware they cannot afford to be involved in the discussion on the negative security effect of biometrics used with a 'fallback password’ required against false rejection/non-match, presumably because there is absolutely no way of eliminating the presence of trade-off relation between false match/acceptance and false non-match/rejection due to the nature of the body features inherent in living animals.
In other words, it looks as though they are afraid that, should they publicly admit the necessity and actual presence of 'fallback measure', a default password/pincode in most cases, the very foundation of their decades-long allegation of “Biometrics brings better security than passwords” would evaporate right away.
As such we are led to suspect that all that the biometrics guys can do is turn a blind eye, cover their ear, close their mouth and keep earning as much quick money as possible before their 'business model' collapses.
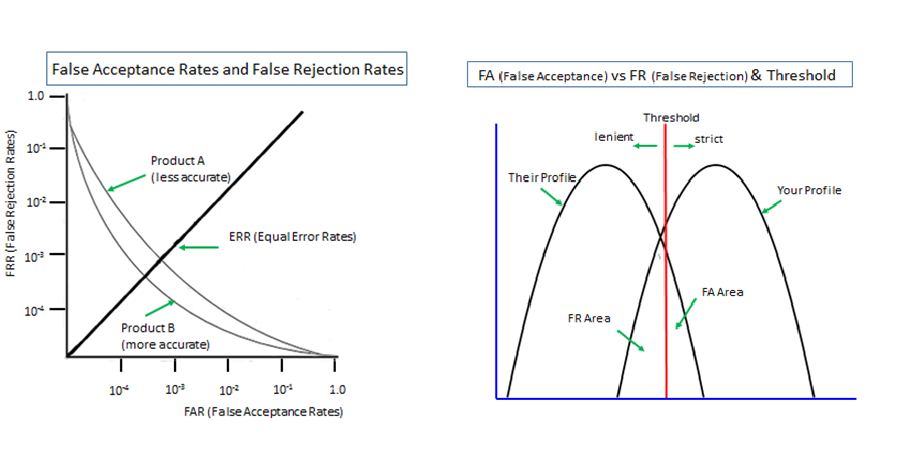
Incidentally, we are also very worried to have noticed that biometrics data is seldom publicized in a logical and scientific manner.
Quite a few biometrics vendors publicize a part of a fact and do not disclose the other part of the fact, for instance, publicizing a nicely low false match/acceptance rate without saying anything about the corresponding false non-match/rejection rate, which could be alarmingly high, but remains unknown to the public.
Subsequently, this phenomenon comes with their silence on the need and presence of a fallback password/pincode against the false non-match/rejection, which brings down security to the level lower than password/pincode-only authentication, as repeatedly made clear in this article.
Moreover, we could add that unsubstantiated theoretical data is often presented as if it were the objective empirical data.
Hitoshi Kokumaiの記事
ブログを見る
Some friends directed my attention to this news report - · “Biometric auth bypassed using fingerpri ...
Biometrics is 'probabilistic' by nature since it measures unpredictably variable body features of li ...

I take up this new report today - “Researchers Defeated Advanced Facial Recognition Tech Using Makeu ...
この職種に興味がある方はこちら
-
英語力を活かす誰もが知ってる大手テ
次の場所にあります: Whatjobs JP C2 - 3日前
株式会社キャリアデザインセンター Tokyo, 日本**お仕事詳細**: · 服装自由 · 残業20時間未満 · 大手・有名企業 · 残業なし · 英語力活かす · 10時以降始業開始 · 派遣社員 · **英語力を活かす誰もが知ってる大手テレビ局で働く/海外ニュースの翻訳**: · お仕事No.66521 · **オススメポイント** · ・残業なし · ・キレイなオフィスでの勤務 · ・社員食堂利用できます · **お仕事内容** · - 大手テレビ局内の国際ニュースを取り扱う部署にて · - 英文資料の日本語への翻訳をお願いします。 · - 【業務詳細】 · - ・海外の通信社から送られてくる英語の ...
-

エステティシャン
次の場所にあります: beBee S2 JP - 1日前
ミュゼプラチナム ながの東急百貨店 長野市, 日本 正社員更新日: · 【業務内容】エステティシャンとしてのサロンワーク全般 · 【雇用形態】 正社員 · 【勤務地】JR信越本線「長野駅」より徒歩4分 · 長野電鉄長野線「長野駅」より徒歩2分(直結)の美容脱毛サロン · 【給与】≪月給内訳≫ · 基本給+職務手当+現場手当 · ※労働時間は所定の時期に変更可能 · ■週休2日(9時間勤務) · 月給 210,000円~ · ■週休2日(8時間勤務) · 月給 190,000円~ · ■週休3日(10時間勤務) · 月給 190,000円~ · ■週休3日(9時間勤務) · 月給 172,000円~ · ■週休 ...
-
全国/フルリモート】バックエンドエンジニア/完全自社開発/医療系サービス
次の場所にあります: beBee S2 JP - 2日前
(株)メドコム Tokyo, 日本主に / TypeScriptを使用したAPIの開発、リードを担当して頂きます。 · 【業務内容】 · ■API開発の計画、設計、開発 · ■フレームワーク・ライブラリのバージョン更新の計画、実施 · ■技術調査、選定 · ■開発方法の方針決め · ■メンバーのフォロー ...

コメント