Update - History, Current Status and Future Scenarios of Expanded Password System
Updated from 30/May/2019 Version
References to the publication of our article by Taylor & Francis and the selection of our proposition as a finalist for“FDATA Global Open Finance Summit & Awards 2019” are added in the chapter of ‘History of Expanded Password System’.
The list of related articles is also updated.
Predicament of Digital Identity
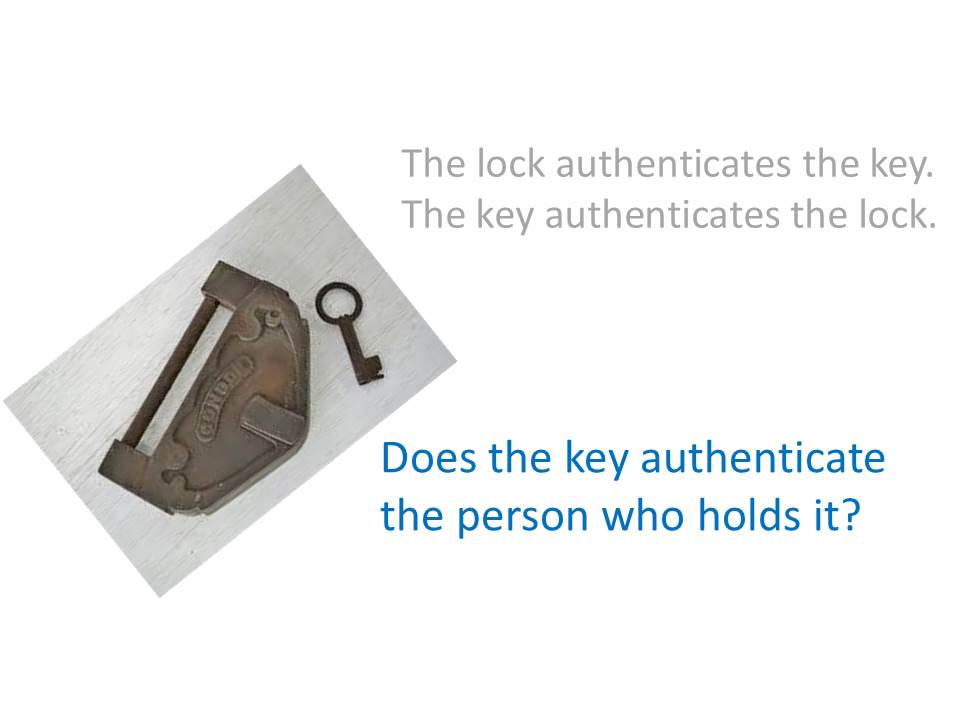
Passwords are so hard to manage that some people are urging the removal of passwords from digital identity altogether. What would happen, then, if the password is removed from our identity assurance?
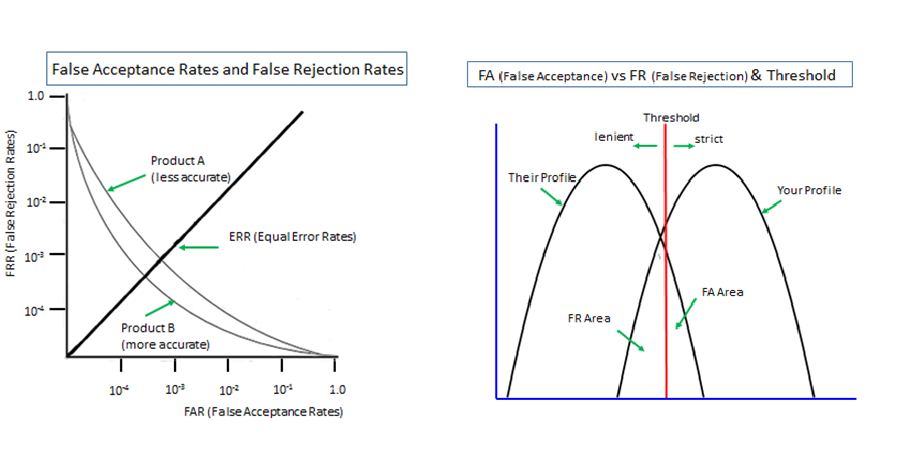
Where the password was kicked out, security providers would be given only the physical token and the biometrics as authentication factors, whereas biometrics requires a fallback measure against false rejection. With the password removed, nothing but the token could be the fallback measure for the biometrics. Then system designer could have only the two choices as follows.
(1) authentication by the token alone, with an option of adding another token. Its security effect is highlighted in this cartoon we published 14 years ago.
(2) authentication by the biometrics deployed in ‘multi-entrance’ method with the token as a fallback measure, security of which is lower than (1) irrespective of however called it may be, with an option of adding another token, as quantitatively explained here.
What a barren desert it would be!
![“Expanded Password System
Bans & Only I can select all of
BL] them correctly
Broader choices with both images and characters accepted
i
Easy 10 manage reletons between accounts and corresponding passwords.
&
Torturous login is hstory. Login is now comfortable, relaxing and heaing
SRO
250
8](https://contents.bebee.com/users/id/13855668/article/update-history-current-status-and-future-scenarios-of-expanded-password-system/e4f1a4d2.png)
Then What Else?
‘Achieving higher-security by removing the password’ and ‘Killing the password by biometrics’ are both no more than the hyped myths. Then, what else can we look to as a valid solution to the predicament of digital identity?
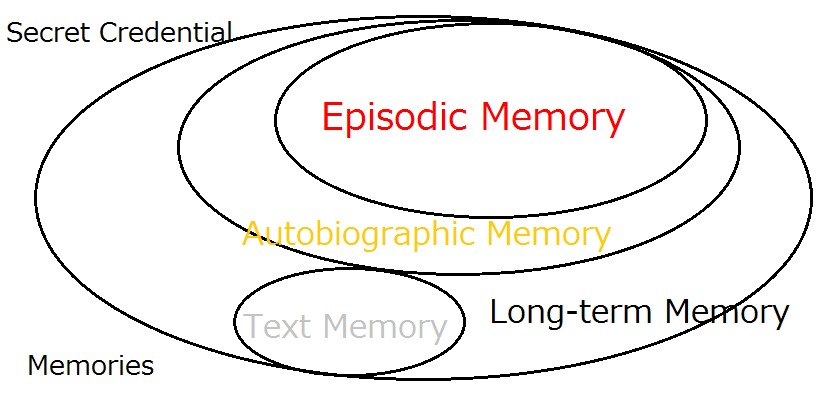
The answer is expanding the password system to accept credentials based on our non-text memories as well as the text memories. We call this proposition ‘Expanded Password System’
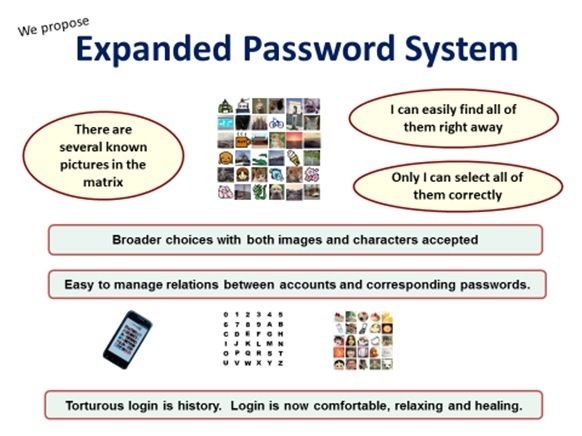
By accepting non-text memories, especially images associated with autobiographic/episodic memories, the Expanded Password System is able to offer a number of excellent features as follows.
- It is not only stress-free for users but fun to use.
- It turns a low-entropy password into high-entropy authentication data
- It eases the burden of managing the relationship between accounts and passwords
- It deters phishing attacks with this unique feature.
- It can be deployed under any type of circumstance, including combat and other panicky situations.
- It supports existing schemes, such as:
- - Biometrics which require passwords as a fallback means
- - Two/multi-factor authentications that require passwords as one of the factors
- - ID Federations such as password managers and single-sign-on services that require passwords as the master-password
- Simple pictorial/emoji-passwords and patterns-on-grid can be deployed on this platform.
- It is relevant whenever text passwords and pin numbers are in use
- And, nothing would be lost for people who want to keep using text passwords
- Last but not least, it continues to rely on free will.
History of Expanded Password System
The concept of this Expanded Password System first came up in 2000. It was followed by the prototyping in 2001 and the commercial implementations from 2003. The history is outlined in this article - How Expanded Password System got this way -
Over the period of 2003 to 2008, the business actually successfully. We saw several commercial adoptions amounting to more than US$1 million, even though handling images was a much heavier task in those days when CPU was slow, the bandwidth narrow and the storage expensive.
It then ceased to grow as people were more and more carried away by the myths of biometrics and password-less authentication which the advocates alleged would kill the passwords altogether, with our proposition included, although we knew that biometrics have to depend on the password as a fallback measure and that a password-less auathentication, if literally implemented, would only bring tragically insecure cyberspace..
After struggling in vain to fight back for several years, we chose to get out of Japan where biometrics vendors were far more dominant than anywhere else, and started to look for bigger chances worldwide. Now, we have some good friends and supporters globally. The writer was invited to speak at KuppingerCole's Consumer Identity World 2018 in Seattle and Amsterdam. Expanded Password System is now acknowledged as Draft Proposal' for OASIS Open Projects.
In 2019 these developments were followed by two outstandingly positive events.
In September Taylor & Francis published our “Digital Identity and Our Remembrance” on its EDPACS (EDP Audit, Control and Security Newsletter) page. Below is the core logic of our discussions.
Assumption: The gains of cyber age would turn against us if connected computers were placed under bad guys’ control. Reliable digital identity is the key to keep off bad guys.
1. Secret credentials are absolutely necessary for digital identity in democratic societies.
2. The text password, which is a section of the secret credentials, is known to be too hard to manage.
3. We could look for something other than the text password as the valid secret credential.
What can be simpler and plainer than this transparent logic? Perhaps only except when being distracted and blinded by vested interests and sunk costs.
Two months thereafter, we were suddenly contacted by Financial Data and Technology Association (FDATA) and invited to present our proposition for “FDATA Global Open Finance Summit & Awards 2019”.
We submitted the proposition on 24/Oct and I was at the Edinburgh summit to receive the honor of being selected as one of the three finalists even though we are not a FDATA member nor related with the organization in any way. It was a dazzlingly rapid development.
Fintech people talk about Open Finance as an enabler of many good things. They talk about Digital Identity as an enabler of the Open Finance and many other good things. They will be talking more about what can really be an enabler of the Digital Identity and we will be making a significant contribution to it with our knowledge and expertise as expressed in our ‘Proposition on How to Build a Sustainable Digital Identity Platform shortlisted for the Summit and Awards 2019”.
Current Status of Business Development
As indicated above, we had come up with not just prototypes but also several commercial products developed for the Japanese clients such as follows:
Client Software for
- Device Login (commercial implementation)
- Applications Login (prototype)
- Image-to-Code Conversion (p)
Server Software for
- Online-Access (c.i.)
- 2-Factor Scheme (c.i.)
- Open ID Compatible (p)
Applied Products: Data Encryption with on-the-fly key generation
- Single & Distributed Authority (c.i.)
None of them, however, are well suited for the services and sales on the global markets, since the programs were all written by Japanese engineers for the Japanese clients with no consideration about the operation, support and maintenance outside Japan.
This also means, however, that we will be able to come up with the products for the global market just easily and quickly with a relatively small budget because algorithms are already here and all that we need to do is to re-write the software in English with the updated cryptography.
For a brief glimpse of what Expanded Password System can offer, watch these brief videos.
Basic Operation - on Smartphone (1m41s)
High-Security Operation - local on PC (4m28s)
Capture and registration of pictures - mapping to long PIN Codes (1m26s)
The readers might also be interested in this comprehensive FAQ -
Future Scenarios
In view of the global nature of our enterprise, we are planning to set up the headquarters in an English-speaking country where we have easy access to the sufficient business and technological resources.
Identity/Security-related businesses who are interested to share the benefits of Expanded Password System could choose one or some of the scenarios as quoted below.
1. Become one of the co-founders of a new business entity that we are going to set up as the global headquarters.
2. Secure a highly privileged status by joining our team at OASIS Open Projects as a voting sponsorship member.
3. Secure some advantageous position by taking part in the active discussions at the OASIS Projects as a non-voting member.
4. Consider other scenarios depending on their aspiration and budget.
* All would depend on their judgement on
- how large or small the enterprise of the now-unknown Expanded Password System could grow and how long or short it could survive and sustain,
- as compared with the now-popular propositions such as ‘password-less authentication’, ‘biometrics as a password-killer’ and ‘physical tokens as a password-killer’,
- as a legitimate successor to the traditional seals, autographs and text-passwords, bearing it in mind that this digital identity enterprise to serve the whole global population could keep a value for social good until humans abandon the digital identity altogether.
< Related Articles >
Text Password System to Stay As-Is with Expanded Password System
Advanced Persistent Threats in Digital Identity
Technology Obsession and Liberal Arts
Negative Security Effect of Biometrics Deployed in Cyberspace
Removal of Passwords and Its Security Effect
#identity #authentication #password #security #fintech #finance #banking #biometrics #ethic #privacy #democracy
Hitoshi Kokumaiの記事
ブログを見る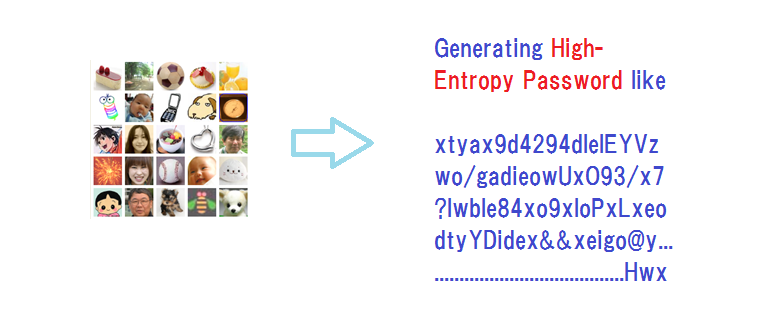
We’ve come up with a slide presentation for “Bring a healthy second life to your legacy password sys ...
Today's topic is this report - “How blockchain technology can create secure digital identities” · h ...
Biometrics is 'probabilistic' by nature since it measures unpredictably variable body features of li ...
この職種に興味がある方はこちら
-
登録販売者
次の場所にあります: Talent JP C2 - 1週間前
ツルハドラッグ 南光台中央店(正社員) Sendai, 日本 正社員仕事情報 · ● 仕事内容 登録販売者の資格や医薬品の販売経験が活かせるお仕事です。ツルハドラッグの店舗にて、医薬品や健康食品などの接客販売、レジ、品出し、商品管理など店内作業全般を行っていただきます。様々な研修制度や充実した福利厚生をご用意しているので、安心して長く働けます。あなたも正社員として活躍してみませんか? ●ツルハグループとは? 日本一のドラッグストアチェーンを目指して、日々成長を続けているツルハグループ。「健康で豊かな暮らしづくりのお手伝い」をモットーに、地域の健康と快適な暮らしを支えています。現在は日本全国とタイに店舗を展開中で、次なる ...
-

保育士
次の場所にあります: beBee S2 JP - 3日前
カナリヤ保育園 町田市, 日本 TEMPORARY【カナリヤ保育園 求人のポイント】 · ◆小田急線 町田駅よりバス15分 · ◆園児定員:33名(0歳~2歳) · ◆時給1,200円~ · ◆認可保育園の保育士 · ----- · 勤務地 · ----- · 東京都町田市山崎町2130 · ----- · 最寄り駅 · ----- · 小田急小田原線町田駅JR横浜線 · 町田駅 · ----- · 園名 · ----- · カナリヤ保育園 · ----- · 施設形態 · ----- · 認可保育園 · ----- · 園児定員 · ----- · 33名 · ----- · 職種 · ----- · ...
-

部品組み立て
次の場所にあります: Whatjobs JP C2 - 3日前
株式会社H&P 堺市 西区, 日本【職種名】 · 修理業務 · **仕事内容**: · 大手釣具メーカー(リール)の修理・メンテナンス業務 · 修理するリールの部品交換やメンテナンスがメインになります。専用の作業台でのもくもく作業。プラモデルが好きな人や、釣りが好きな人にオススメです。 · まずは丁寧に教えていきますので安心してくださいね · 慣れてくれば、どんどん収入もアップできます。 · - 空調完備室内での専用席(座り仕事) · - もくもく作業で自分の仕事に集中できる · - やる気がある人は稼げるインセンティブ制度 · - 充実した丁寧な育成 · - 未経験大歓迎 · - 大手 ...
&v=024)
コメント