Global Headquarters in United Kingdom

Having been talking for some time about the headquarters to be set up for global operations of Expanded Password System (EPS), we have now chosen UK as the venue in view of its reputed R&D infrastructure.
We are putting together diverse brains from multiple disciplines - psychology, sociology, behavioral economics as well as tamper-proof programming, cryptography and other security-intelligence technologies in the common language in view of our mission of globally promoting identity assurance by our own volition and memory for secure digital identity in post-pandemic cyberspace,
The aim of our enterprise is to make EPS solutions readily available to all the global citizens: rich and poor, young and old, healthy and disabled, literate and illiterate, in peace and in disasters.
Here is a summary and brief history of Expanded Password System since 2000 when I first thought of making use of our episodic image memory for identity authentication. Key references are mentioned in it.
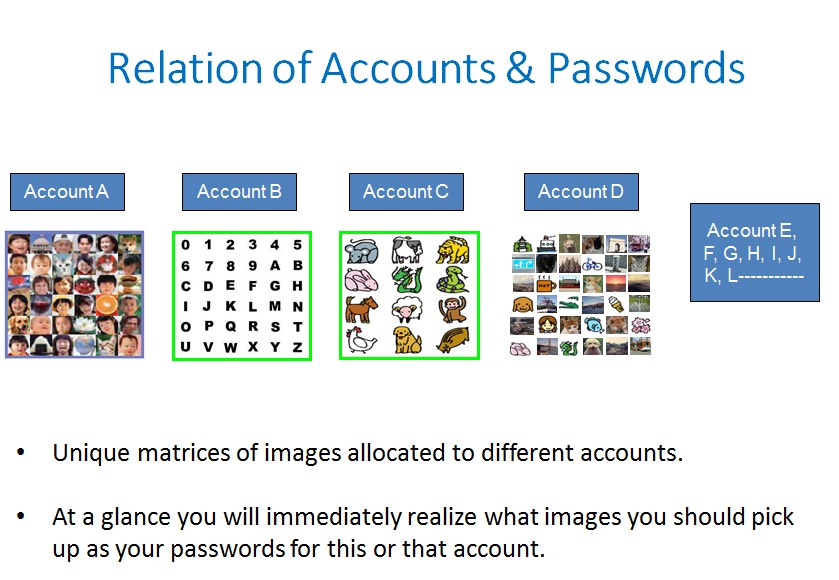
Identity Assurance - Sufficient and Necessary Conditions
It is not easy to define the 'sufficient condition' for describing a set of processes used to establish that a natural person is real, unique, and identifiable; criminals keep coming up with hitherto unknown weapons to compromise the said processes.
But we are easily able to define the 'necessary condition'; it is that the 'secret credential', i.e., the likes of passwords, is absolutely indispensable for the processes to stay reliable.
Let us summarize the characteristics of the factors for the processes, namely, the authenticators, as follows.
1. Secret credentials are absolutely indispensable, without which identity assurance would be a disaster. (Ref. Removal of Passwords and Its Security Effect )
2. Two-factor authentication made of passwords and tokens provides a higher security than a single-factor authentication of passwords or tokens. (Ref. Quantitative Examination of Multiple Authenticator Deployment )
3. Pseudo two-factor authentication made of biometrics and a password brings down the security to the level lower than a password-alone authentication. (Ref. Negative Security Effect of Biometrics Deployed in Cyberspace )
4. Passwords are the last resort in such emergencies where we are naked and injured (Ref. Availability-First Approach )
5. We could consider expanding the password systems to accept both images and texts to drastically expand the scope of secret credentials. (Ref. Proposition on How to Build Sustainable Digital Identity Platform )
We could add the following.
‘Easy-to-Remember’ is one thing. Hard-to-Forget’ is another - The observation that images are easy to remember has been known for many decades; it is not what we discuss. What we discuss is that ‘images of our emotion-colored episodic memory’ is ‘Hard to Forget’ to the extent that it is ‘Panic-Proof’. This feature makes the applied solutions deployable in any demanding environments for any demanding use cases, with teleworking in stressful situations like pandemic included.
Hitoshi Kokumaiの記事
ブログを見る
Today's topic is this report - “How blockchain technology can create secure digital identities” · h ...

I today take up this The Register report - “Client-side content scanning as an unworkable, insecure ...

I take up this new report today - “Researchers Defeated Advanced Facial Recognition Tech Using Makeu ...
この職種に興味がある方はこちら
-

塾講師 アルバイト 個別指導
次の場所にあります: beBee S2 JP - 5日前
栄光の個別ビザビ 池上校 大田区, 日本 パートタイム雇用形態 · アルバイト · 職種・指導形態 · 個別指導 · ≪講師1人に生徒は2人までの個別指導≫ · 長机の真ん中に講師、両隣に生徒が座る授業形式です。 · 講師自身が移動することはないので、 · テキストを広げながら落ち着いて指導することができます。 · 給与 · 1コマ80分1,980円 · 時給1,200円~ · 1コマ(80分)1,980円~ (授業前後手当含む) · <1日の給与例> ※授業前後手当を含む · ・1コマ(80分)×2コマの場合 3,770円~ · ・1コマ(80分)×3コマの場合 5,560円~ · ◆授業前後手当 (1日 ...
-

塾講師 アルバイト 個別指導
次の場所にあります: beBee S2 JP - 4日前
ECCベストワン JR茨木校 茨木市, 日本 パートタイム雇用形態 · アルバイト · 職種・指導形態 · 個別指導 · 講師1人:生徒1人もしくは、講師1人:生徒2人の個別指導 · 給与 · 1コマ90分1,700円〜3,000円 · 週2勤務で月に4万円以上稼ぐことも可能です · ◇コマ給以外にも各種手当あり◇ · ・体験授業成功手当→3000円 · ・生徒紹介手当→3000円 · ・講師紹介手当→10000円 · 最寄駅 · 茨木〔JR〕駅より徒歩5分 · 宇野辺駅より徒歩12分 · 茨木市〔阪急線〕駅より徒歩23分 · 待遇 · ・能力、経験によりコマ給優遇あります。 · ・交通費全額支給(規定あり) ...
-
パート】幼稚園・保育園の調理補助 ♪子ども達の笑顔がやりがいです♪
次の場所にあります: Talent JP C2 - 5日前
高円寺りとるぱんぷきんず Suginami, 日本お仕事情報 · お仕事内容 家庭と無理なく両立できると主婦さんに好評♪ · 普段の家事を活かして働きませんか? · ▼ご担当していただくお仕事 · 食材の仕込み作業をはじめ、 · 調理全般・味付け・盛り付け等をお願いします。 · まずは先輩スタッフのお手伝いをしながら、 · 職場の雰囲気やお仕事の流れを掴んでいきましょう♪ · 給与 時給 1250円以上 · ◆昇給あり · ◆支払い方法:月1回 · ◆交通費:一部支給 · 所在地 東京都 杉並区 高円寺北1-27-3 · アクセス ◆中央線 高円寺駅 徒歩 10分 · 勤務期間 長期(3 ...

コメント