Cult of Convenience
New writing "What actually tells ‘probabilistic authenticator’ and ‘deterministic authenticator’ apart? " and "Cult of Convenience" are added at the end of "Negative Security Effect of Biometrics Deployed in Cyberspace"
..............................................
Cult of Convenience
It is natural for us to be thankful to the people who came up with the means to safely get the job done in one day that used to take weeks or months to do unsafely.
Who could be thankful to the people who come up with the means to unsafely get the job done in 5 seconds that used to take 10 seconds to do safely? If any, we could call them ‘Cult of Convenience’. Such a behavior could be viewed as ‘time-saving obsession syndrome’. Actually, we know there are many of them in the sphere of cybersecurity and identity management.
Putting a finger on a sensor or holding a smartphone in front of our face may look a bit more ‘time-saving’ as compared with feeding numbers and characters, This ‘time-saving’ effect is obtained, however, by taking the risk of a huge inconvenience or time-wasting trouble in case of the leakage of the body feature data.
The cult of convenience would not care. For them, the few seconds thus saved is worth the grave risk of leakage of the privacy data that people can never cancel, change or re-generate for life.
And, alas, all this happens on top of the fact that the use of biometrics brings down security to the level lower than a PIN/password-only login.
What on earth are we doing?
What actually tells ‘probabilistic authenticator’ and ‘deterministic authenticator’ apart?
Some people appear to be led to assume that there are a FAR and an FRR with any means of authentication. I am afraid that they are misguided.
‘Acceptance and Rejection’ of a deterministic tool (Yes or No on remembrance of a correct password and Yes or No on possession of a correct physical token) is one thing, that of a probabilistic tool (biometrics to measure unpredictably variable body features) is another.
As a matter of fact, a password and a physical token can be and are actually used together in a security-enhancing ‘multi-layer’ deployment because these are both deterministic, whereas biometrics and password/token can be and are actually used together only in a security-lowering ‘multi-entrance’ deployment because biometrics is probabilistic. Mixing up those fundamentally different subjects would be very misleading.
The analysis of biometrics being probabilistic leads us to the next observation that 'biometrics-only authentication' could exist only on paper, because the users who get rejected due to the unpredictable false rejection would have only choice of giving up the login altogether. It cannot be allowed in our real life.
Hitoshi Kokumaiの記事
ブログを見る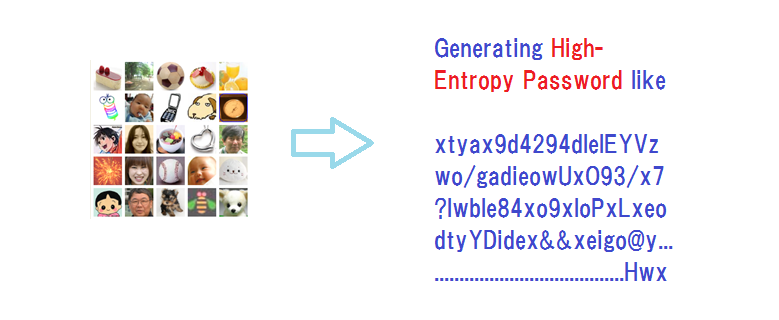
“Expanded Password System is no bad, but we do not need it. · We can rely on password managers that ...
We’ve come up with a slide presentation for “Bring a healthy second life to your legacy password sys ...

Another topic for today is “Passwordless made simple with user empowerment” · https://www.securitym ...
この職種に興味がある方はこちら
-

ゲームテスターデバッカー
次の場所にあります: Whatjobs JP C2 - 2日前
株式会社アヴニール Tokyo, 日本【職種名】 · ゲームテスター/デバッカー · **仕事内容**: · ゲームテスター募集 ゲーム好きのあなた、夢を仕事にしませんか? · ゲームが大好きで、将来はゲーム業界で働きたいあなた · ■ 未経験者でも安心 充実した研修制度でスキルアップ · ゲーム業界に興味はあるけど、知識も経験もない · そんなあなたでも大丈夫 弊社は充実した研修制度で、未経験者からゲームテスターとして活躍できるようサポートします。 · 【研修内容】 · 3ヶ月間、経験豊富な講師が丁寧に指導します。 · ・ゲーム業界の基礎知識 · ・テストに必要なスキル · ・ゲームの動作 ...
-

Especialista en marketing Español
次の場所にあります: beBee S2 JP - 1週間前
ZenGroup INC Osaka, 日本◆Duties · ・PPC advertisements (GDN, Meta ads, etc) · ・SNS management · ・Influencer marketing · ・Content Marketing ( blogs, keyword research, SEO) · ・Data analysis (Google analytics etc.) · ・Email marketing · ・English to Spanish localization · ◆Sample day at work · 9~10 Morning ro ...
-

学習指導、教室運営
次の場所にあります: Whatjobs JP C2 - 4日前
公文教育研究会 神奈川ブランチ 横浜市 西区, 日本**公文教育研究会 神奈川ブランチ** · **「くもんの先生」始めませんか?資格・経験不問研修あり/各種援助制度あり** · (応募可能期間 :2023/09/01 ~ 2023/09/28) · **・給与** · (報酬)収入は生徒数により異なります(出来高制) · 各種援助制度あり · 実子は公文式会費全額免除 · **・職種** · 学習指導、教室運営 · **・勤務地** · 横浜市内各地 · **・こだわり条件** · 未経験者歓迎 · 子育て支援 · 大手企業・公的機関 · ‐‐‐‐‐‐‐‐‐‐ · - 学習指導経験がない方もOK · あ ...
コメント